There is increasing discussion around no-code and low-code engines as they enable agility and customization with the same output as an in-house expert developer. A no-code rules engine makes it possible for businesses to run their back end as well as their front end infrastructure exactly as they want, and to make quick alterations to rules to reflect changing needs.
When it comes to fraud, this quick reaction is especially necessary as the risk landscape for a any digital service continually moves, but how would this work? We deep dive into our own no-code fraud rules engine to explain.
The traditional fraud rules engine
Typically, a fraud manager will design various rules in a document that gets handed to the engineering team to build. From scratch, the rules and requirements are coded over anything from a few days to a few weeks depending on their complexity and the engineering resources which other areas of the business are competing for. Additionally, before deployment, the rules need to be tested vigorously to ensure that they meet their designed goal as well as ensuring they don’t interfere with other parts of the business' infrastructure or weaken existing rules.
With engineering time often being so scarce and difficult to manage, fraud teams are often left managing risk while the rules are built out by another team. This leaves a hole in cohesiveness and a holistic understanding of what is currently working (or not working), and how new rules need to be coded for stronger results.
Authsignal’s no-code fraud rules engine
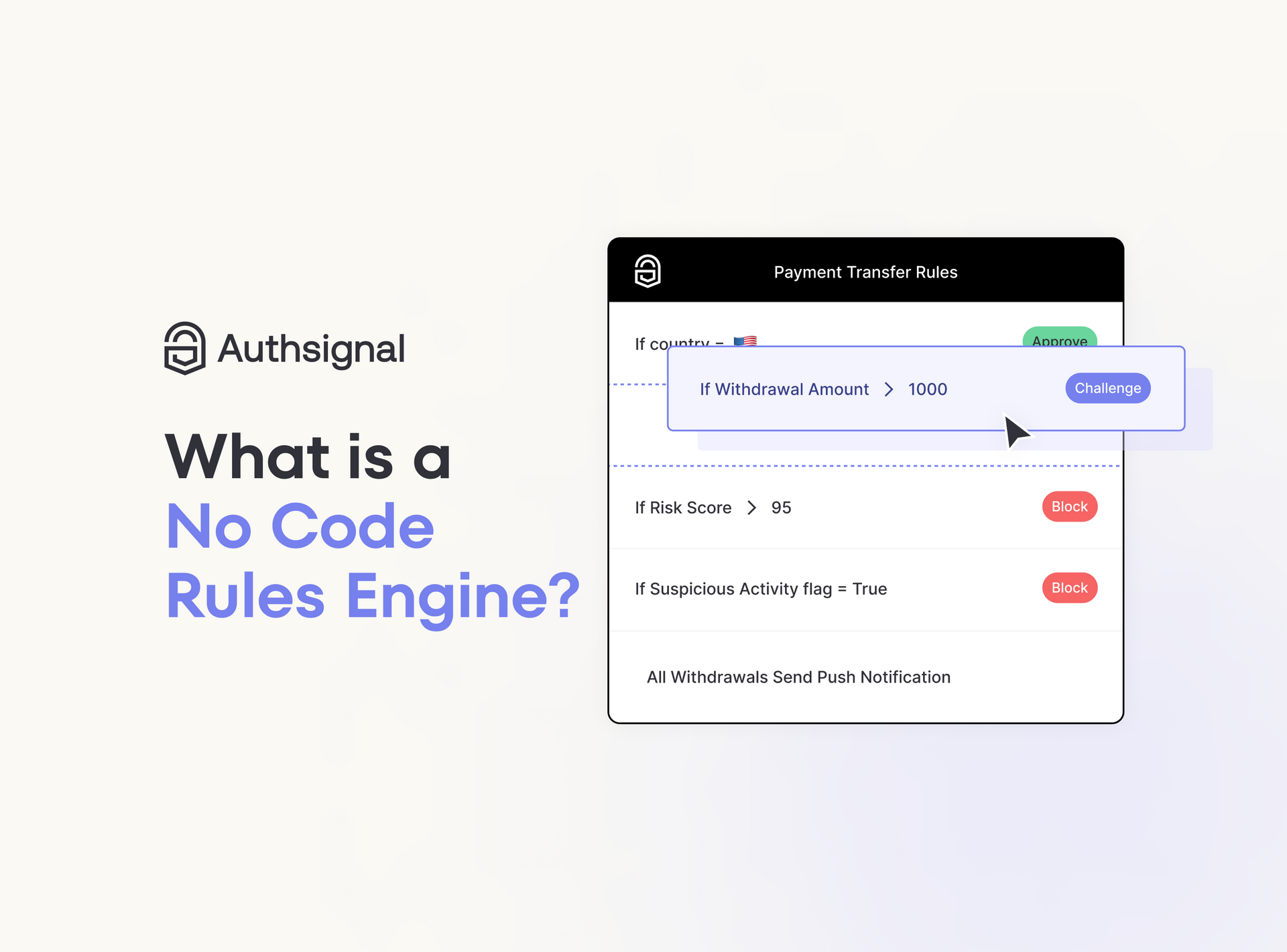
At Authsignal, we created a no-code fraud rules engine to enable FraudOps teams to design their own rules, deploy and manage them, taking away the need for engineers to build them. Understanding how insights drive changes and vice versa, our no-code rules engine for FraudOps enables the team to adapt as they see their risks change.

With the ability to create rules catering to IP, location, and the last authentication time frame, to name a few, each rule can include as many or as few elements so that businesses are able to target their most riskiest attempts even as they move.
As each platform finds a trend in their attacks or attempted attacks, with Authsignal’s no code fraud engine, they are able to get granular in their rules to stop these from happening again. For example, if insights show that a specific IP address that tends to try to gain access every other day is recurring, the rules engine can build a rule to target them by blocking them entirely.

Another rule example is using time and location as a factor. Where one user is shown to login from two locations that would be physically impossible to travel between, the engine can challenge the attempts and request for further verification.

There is flexibility in Authsignal’s no code fraud engine as shown by the ability to block or challenge a sign in attempt, as well as other features that allow for business-specific data to be utilised and dictate the rule. As the platform allows for easy integration with existing data and dropdowns and buttons to include them into a single rule, fraud teams really can create and deploy rules within a matter of hours.
How Authsignal’s no code fraud rules engine differs
The Authsignal no code fraud rules engine is intuitive and simple to use, and we designed it this way so that FraudOps can truly manage it themselves. Toggles, drop down lists and customised bars are included so that the rules created are strategic and relevant to your unique risk profile, but also so that it’s clear both from the start and for anyone jumping in to take a look, what the rule actually does.
The Authsignal rules engine is entirely designed around fraud use cases and requirements meaning that we have considered the multiple ways in which fraud can seep into a business and the necessary precautions required to stay one step ahead at every touch point. We have a library of pre-built rules that can help an early stage business or one light on resources and expertise to get started, however these can also be customised so it continues to work best with your own application.
With our own experience in fraud, we designed our rules engine to withstand high transaction velocity so your business is kept secure and the data intact no matter how much volume you see. For a busy, high traffic business this is critical for continuity as well as maintaining compliance meaning your business and customers are kept safe even when under attack.
The Authsignal no code fraud rules engine also allows teams to add custom data signals for even greater control and detection. As mentioned, one of the data points is travel whereby the fraud rules engine looks at two sign-ins that originate from geographically distant locations. By taking into account the time between sign ups and using algorithms to understand the behaviors of a new user, the engine learns what is and isn’t usual and how best to protect the business.
In summary: the no code fraud rules engine
The no code fraud rules engine is the smartest way to protect your platforms because not only is it the quickest to implement new rules, but by providing teams with the ability to manage their own rules means that FraudOps can remain agile and reactive in today’s incredibly fast-paced environment.
The Authsignal no code fraud rules engine benefits from a marketplace of fraud and risk providers giving access to AI and machine learning, as well as an intuitive design for code deployment and ongoing risk assessment. It empowers teams and organizations in their continued fight against attacks and malicious actors without adding further strain onto already precious resources.